Scyld Cloud Portal¶
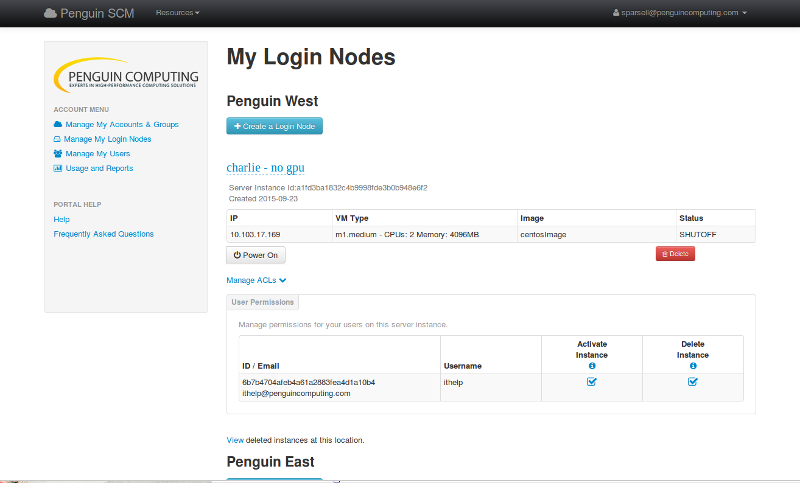
The SCM portal is a web-based user interface that enables a user to create and manage virtual machines, called server-instances, along with optional management of storage volumes, Unix users and groups, and SSH keys. The SCM portal also enables robust reporting of server-instance utilization and, when enabled, storage and compute cluster core-hour utilization. This is a sample screen image:
All capabilities present within the SCM portal are built upon the SCM APIs, which are documented in the “SCM API Guide.”
Scyld Cloud Portal Settings¶
Configuration settings for the Scyld Cloud Portal can be found
in the cloudportal.ini file.
See the cloudportal.ini file for an exhaustive list of settings
along with explanations;
in most cases the default value is appropriate.
User Registration/Login¶
New users are created by registering on the portal.
There are two workflows defined:
LDAP integration and self-registration with email validation.
The preferred workflow is indicated in the settings file
(cloudportal.ini) via the userauth.driver setting.
Other important registration settings are:
registration.type- Leave blank for unrestricted registration or specifywhitelistto indicate whitelist-restricted registrationdefault_user_role- Leave blank or set toaccount_owner. See roles for more information.
LDAP Integration¶
When using LDAP as an authentication and authorization backend, users bypass registration and simply log in to the portal. If it is their first login, some setup occurs transparently to the user. Their cloudauth account is established and any default roles or SCM resources are configured.
Administrators may use LDAP attributes to limit SCM access by specifying a group DN in the ldap settings (ldap.auth_require_group). Only users belonging to this group may access the portal and SCM resources. If site-wide system (Unix) usernames are maintained in LDAP, the ldap.uname_attr setting should indicate the attribute name.
Important LDAP settings are listed below:
ldap.hosts- Space-separated list of ldap serversldap.timeout- Timeout, in seconds, before the next server in the list of ldap.hosts is tried.ldap.cert_file- Path to TLS certificate.ldap.cacert_file- Path to TLS certificate chain file.ldap.cacert_dir- Path to directory of TLS certificates.ldap.bind_uname- Username of LDAP bind user.ldap.bind_pw- Password for bind user.ldap.user_search_dn- Search string for use in resolving a user DN.ldap.uid_attr- LDAP attribute name for the userid.ldap.mail_attr- LDAP attribute for the user’s email address.ldap.require_group- Groupname if group membership is required.ldap.require_attr- LDAP attribute name that must be valued, if listed, for LDAP eligibility.ldap.uname_attr- LDAP attribute indicating user’s system username.
Single Sign-On¶
When using a SAML Single Sign-On (SSO) for authentication and authorization, users bypass registration and simply log in to the portal. If it is their first login, some setup occurs transparently to the user. Their cloudauth account is established and any default roles or SCM resources are configured.
Any user who is able to reach the portal will be allowed access. The SSO Identity Provider must limit access.
SSO login must also be enabled in Scyld Cloud Auth.
Important SSO settings:
auth_sso- Boolean, defaults to False. Must be True for SSO logins.auth_sso.admin_attributes- Default is no attributes. Takes a string of newline-separated key = value entries.
auth_sso.admin_attributes checks the SAML attributes for a key/value match. If a key has multiple values, each value will be checked. On a match, the user will be able to escalate to the admin local account after logging in by clicking the Log in as admin link in the sidebar.. Logging out will return them to their standard profile.
Example:
auth.sso.admin_attributes = role = manager@samltest.id
role = admin@samltest.id
Integration with the Shibboleth Service Provider is discussed in Shibboleth as Service Provider.
Self Registration¶
In this workflow, users register for an account by filling out some basic user information after validating their email address.
Registration Whitelist¶
The registration.type setting, if set to whitelist will enable the administrator to restrict the ability to register to a specific list of users. This setting may be applied when either registration workflow is used. The “Manage Whitelist” link in the administrative menu will allow the administrator to manage this list.
CloudController Integration¶
Each SCM installation will have at least one cloudcontroller instance. Each cloudcontroller that the portal will communicate with needs to be listed in the cloudportal.ini file with its particular id.
cloudcon.<id>.driver- Leave this setting “scm”. Other values are strictly for testing.cloudcon.<id>.name- The name displayed in the portal for this cloudcontroller.cloudcon.<id>.description-The description of this cloudcontroller.cloudcon.<id>.api_version- Cloudcontroller API version number.cloudcon.<id>.api_endpoint- hostname:port for the cloudcontrollercloudcon.<id>.api_ssl- Whether or not the cloudcontroller uses SSL.cloudcon.<id>.report_queues- A space-separated list of scheduler queues to be visible in the portal, if supported (i.e. cluster integration exists)
Other SCM Options¶
Other options include the ability for SCM to support integrated storage and support for ssh key management when supporting public key access to VMs. Relevant settings are listed here:
scm.ssh_key_mgmt- Support for ssh key managementscm.storage_mgmt- Support for storage integration.scm.cc_storage_driver- Type of storage support.
Scyld Cloud Workstation Integration¶
If the login nodes are running Scyld Cloud Workstation, authentication can be performed through the cloudportal.
scw_token_login- Defaults to False. If True, Scyld Cloud Workstation-enabled login nodes will be accessible through the instances page. Click the SCW Login button for the desired login node.scw_token_login.masq_allowed- Defaults to False. When False, the SCW Login feature will be unavailable when the admin profile or other superusers are masquerading as another user.
Full documentation of Scyld Cloud Workstation is available at https://updates.penguincomputing.com/scw/scyld-cloud-workstation/
The following settings for SCW on the login node are required:
Server.Auth.ScyldCloudAuth.URL- the Scyld Cloud Auth URL.Server.Auth.ScyldCloudAuth.ApiSecret- the SCW admin account API key.Server.Auth.ScyldCloudAuth.ApiSecret- the SCW admin account API secret.
Suggested settings:
Server.Auth.ExternalSignInPage- add the cloudportal URL to disable username/password logins and point logged out users back to the cloudportal.Server.Auth.OSAuthEnabled- set to False to disable login using login node’s operating system authentication.
Portal Branding and Customization¶
Customizing the look and feel of the SCM portal is possible using the settings
in the cloudportal.ini file. Details about usage and format can be found in the ini file.
site.title- appears in the top navigation bar and default page titlesite.logo- logo file in the main page templatesite.sidebar_lower- content (html format) that appears in lower sidebar typically used to display links to external resources, documentation, etc.site.login_help_message- message appears on login page
Further customization is possible by editing the site templates directly. The site templates use a python library called mako. Care must be taken to avoid syntax errors which may result in broken pages or server errors.